Islamabad, Mar 5, 2025: The National Computer Emergency Response Team (National CERT) has issued a crucial warning about a widespread phishing attack leveraging fake CAPTCHA images in PDF files to distribute Lumma Stealer malware.
This large-scale cyber threat has compromised thousands of individuals and organizations across industries such as technology, finance, and manufacturing
Hackers are employing search engine manipulation tactics to spread these infected PDF files
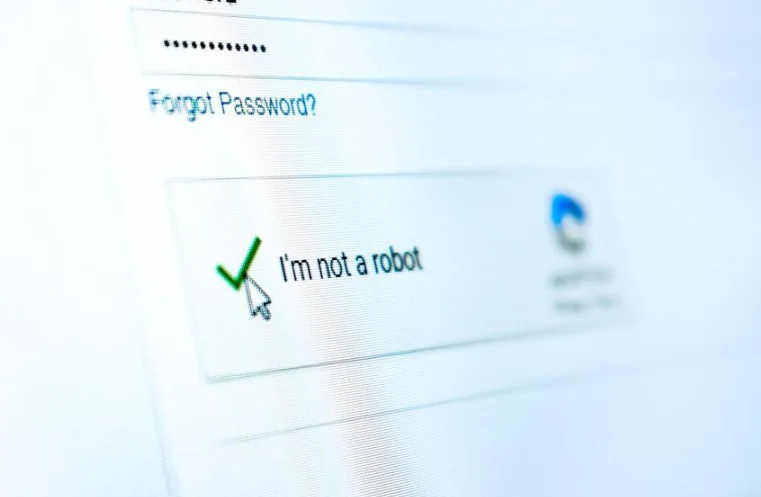
The attack relies on deceptive CAPTCHA images within the PDFs that trick users into clicking malicious links, leading them to phishing pages.
These fraudulent sites either extract sensitive banking details or deploy PowerShell scripts via MSHTA commands to install the Lumma Stealer malware covertly.
Attackers are hosting these harmful PDFs on platforms such as PDFCOFFEE, PDF4PRO, and Internet Archive.
Lumma Stealer operates as a Malware-as-a-Service (MaaS) tool, capable of extracting login credentials, browser cookies, and cryptocurrency wallet information.
Read More:
Nothing Phone 3a & 3a Pro: Best Affordable Flagships Yet?
Additionally, it deploys GhostSocks, a proxy malware that hijacks victims’ internet connections.
Stolen credentials are being sold on underground cybercrime forums like Leaky[.]pro. Malicious domains linked to this campaign include pdf-freefiles[.]com, webflow-docs[.]info, secure-pdfread[.]site, and docsviewing[.]net.
To combat this evolving cyber threat, National CERT has issued security recommendations for organizations and individuals.
Key measures include educating employees on recognizing phishing attempts, implementing advanced endpoint security, and restricting PowerShell and MSHTA execution to minimize risk.
Experts advise companies to block known malicious domains, enable PowerShell activity logging, and enforce multi-factor authentication (MFA) to protect credentials.
Monitoring search engine results for deceptive domains mimicking trusted services is also essential.
With cybercriminals continuously refining their attack strategies, organizations must adopt proactive cybersecurity practices.
Essential measures include regular security patching, limiting administrative access, and employing application whitelisting.
As cyber threats grow more sophisticated, staying alert and reinforcing security frameworks is vital to preventing data breaches
However, Vigilance and a robust defense strategy remain the best shields against these emerging cyber risks.